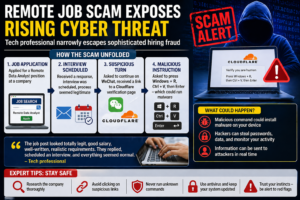
New Delhi: In an alarming example of how cybercriminals are evolving their tactics, a seemingly routine job application for a remote position has exposed the growing sophistication of online recruitment scams. A technology professional recently shared his experience of narrowly escaping a well-crafted cyber fraud, shedding light on how even experienced individuals can fall prey to deceptive digital schemes.
The incident has sparked widespread concern across online communities and cybersecurity circles, as it demonstrates how scammers are increasingly mimicking legitimate hiring processes to exploit job seekers.
A Convincing Beginning: When Fraud Looks Real
The victim, a tech professional with industry experience, had applied for a Remote Data Analyst role at a company that appeared entirely legitimate. The job listing included all the hallmarks of authenticity:
- A competitive salary package
- Clearly defined job responsibilities
- Requirements aligned with industry standards
- Professional language and formatting
At no point during the initial stages did anything appear suspicious.
Shortly after applying, the candidate received a response from the purported employer. An interview was scheduled, and communication continued in a structured and professional manner. The process closely resembled standard hiring workflows followed by reputable organizations.
Reflecting on the experience, the individual later shared online that everything “seemed normal” and consistent with legitimate recruitment practices.
The Illusion of Legitimacy
One of the most concerning aspects of this case is the level of detail and authenticity in the scam. Cybercriminals have clearly studied real hiring processes and replicated them with precision.
The communication included:
- Prompt email responses
- Formal interview scheduling
- Professional tone and language
- Step-by-step guidance throughout the process
This level of sophistication significantly lowers suspicion, especially for job seekers actively looking for opportunities.
Experts warn that such scams are no longer limited to poorly written emails or obvious red flags. Instead, they now involve carefully orchestrated interactions designed to build trust over time.
The Turning Point: A Suspicious Instruction
The situation took a dangerous turn during what appeared to be a routine verification step. The candidate was directed to continue the process through a link shared on WeChat, a widely used messaging platform.
Clicking the link led to a page that resembled a standard security verification interface, similar to those used by Cloudflare. Such pages are commonly used to confirm that a user is human and to prevent automated bot activity.
However, this page behaved differently.
The candidate was instructed to perform a sequence of keyboard actions:
- Press Windows + R
- Then press Ctrl + V
- Finally, hit Enter
Unbeknownst to the user, the page had automatically copied a malicious command to the system clipboard. Executing these steps would have triggered malware installation on the device—without any visible warning.
How the Malware Attack Works
Cybersecurity experts explain that this type of attack leverages a technique known as “clipboard injection.” By silently copying malicious code onto a user’s clipboard, attackers trick victims into executing commands themselves.
Once activated, the malware can:
- Steal saved passwords from browsers
- Access sensitive personal and financial data
- Monitor user activity in real time
- Transmit information to remote attackers
Such malware is often categorized as “infostealer” software, which is specifically designed to harvest confidential data.
The danger lies in its invisibility—users may not even realize their system has been compromised.
A Narrow Escape
Fortunately, the tech professional sensed something was wrong before executing the instructions. The unusual requirement to use system commands for a simple verification step raised suspicion.
This hesitation likely prevented a serious data breach.
Later, the individual shared the experience online as a warning to others, emphasizing how easily the situation could have resulted in a major cyberattack.
Why This Scam Is Particularly Dangerous
What sets this case apart from traditional scams is its ability to mimic trusted systems. The use of a fake Cloudflare verification page is especially concerning because such pages are widely recognized as legitimate security measures.
By exploiting this familiarity, attackers lower the user’s guard and increase the likelihood of compliance.
Cybersecurity professionals highlight several reasons why this scam is particularly effective:
- It targets job seekers, who are already motivated and engaged
- It uses trusted platforms and tools
- It introduces malicious steps gradually
- It avoids obvious warning signs until the final stage
Social Media Reactions: Awareness and Criticism
The incident quickly gained attention on social media, prompting a mix of concern, advice, and criticism from users.
Some individuals warned about the serious последствия of executing such commands, noting that even if passwords are changed later, compromised systems may continue to transmit data.
Others pointed out that the instructions should have raised immediate red flags, emphasizing the importance of basic cybersecurity awareness.
Despite differing reactions, the consensus was clear: such scams are becoming increasingly sophisticated and dangerous.
The Growing Threat of Job Scams
Online job scams have seen a significant rise in recent years, particularly with the increase in remote work opportunities. Cybercriminals are exploiting this trend by creating fake job listings and impersonating recruiters.
Common tactics include:
- Fake job postings on legitimate platforms
- Phishing emails posing as HR representatives
- Requests for personal or financial information
- Malicious links disguised as application portals
The shift toward remote hiring has made it easier for scammers to operate without face-to-face interaction, increasing the risk for job seekers.
Psychological Manipulation in Recruitment Scams
These scams rely heavily on psychological manipulation. By offering attractive job opportunities, attackers tap into the hopes and aspirations of candidates.
They build trust through:
- Professional communication
- Timely responses
- Structured processes
Once trust is established, victims are more likely to follow instructions without questioning them.
Red Flags Every Job Seeker Should Know
Experts recommend being alert to the following warning signs:
- Requests to perform unusual technical actions
- Communication through unofficial platforms
- Lack of verifiable company information
- Pressure to act quickly
- Requests for sensitive data early in the process
In this case, the instruction to execute system commands was a critical red flag.
Cybersecurity Best Practices
To protect against such threats, individuals should follow basic cybersecurity guidelines:
- Never run unknown commands on your system
- Verify company details through official websites
- Avoid clicking suspicious links
- Use updated antivirus software
- Enable multi-factor authentication
Awareness and caution are key to preventing cyber fraud.
The Role of Tech Companies and Platforms
Companies and online platforms also have a responsibility to address this growing issue. Measures that can help include:
- Improved verification of job listings
- Monitoring for suspicious activity
- Educating users about common scams
Collaboration between tech companies and cybersecurity experts is essential to combat these threats.
A Wake-Up Call for the Digital Workforce
This incident serves as a stark reminder that cyber threats are evolving rapidly. Even individuals with technical knowledge can be targeted through cleverly designed scams.
As digital interactions continue to replace traditional processes, the need for vigilance becomes even more critical.
Our Media Opinion: Staying One Step Ahead
The near-miss experienced by this tech professional highlights the awareness in today’s digital landscape. While the scam was sophisticated, it was ultimately a moment of caution that prevented a potentially serious breach.
As cybercriminals continue to refine their methods, individuals must remain informed and alert. Recognizing red flags, questioning unusual instructions, and prioritizing cybersecurity can make the difference between safety and compromise.
The lesson is clear: in the digital age, even the most routine processes can conceal hidden risks—and staying vigilant is the best defense.